I noticed the growing security concerns around MCP (https://news.ycombinator.com/item?id=43600192) and built an open source tool that can detect several patterns of tool poisoning attacks, exfiltration channels and cross-origin manipulations.
MCP-Shield scans your installed servers (Cursor, Claude Desktop, etc.) and shows what each tool is trying to do at the instruction level, beyond just the API surface. It catches hidden instructions that try to read sensitive files, shadow other tools' behavior, or exfiltrate data.
Example of what it detects:
- Hidden instructions attempting to access ~/.ssh/id_rsa
- Cross-origin manipulations between server that can redirect WhatsApp messages
- Tool shadowing that overrides behavior of other MCP tools
- Potential exfiltration channels through optional parameters
I've included clear examples of detection outputs in the README and multiple example vulnerabilities in the repo so you can see the kinds of things it catches.
This is an early version, but I'd appreciate feedback from the community, especially around detection patterns and false positives.
Comments URL: https://news.ycombinator.com/item?id=43689178
Points: 49
# Comments: 12
Login to add comment
Other posts in this group
Earlier today Cursor, the magical AI-powered IDE started kicking users off when they logged in from multiple machines.
Like,you’d be working on your desktop, switch to your laptop, and all of a
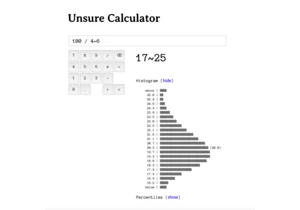
Article URL: https://filiph.github.io/unsure/
Comments URL: https://news.ycombinator.c


Article URL: https://www.csoonline.co