Elastic Cloud customers can now ingest data more simply, quickly, and securely, and the latest updates to the core Elastic Stack provide users with new tools for maximizing performance and exploring their data. The 7.15 release of Elastic Cloud brings new integrations with Google Cloud that allow customers to ingest Google Cloud services data directly into their Elastic Cloud deployments and take advantage of additional network security with Google Cloud Private Service Connect. Plus, the Elasti
Elastic Enterprise Search 7.15 introduces general availability for App Search’s web crawler making it quick and effortless to spin up powerful, new search experiences for every use case.
We’re also adding countless ways to personalize Workplace Search to meet the unique needs of your organization with the ability to add custom branding, schedule sync frequency, and configure automatic filter detection. These updates help teams launch search faster and tailor the search experiences they create
We are pleased to announce the general availability of Elastic 7.15, a release that brings a broad set of new capabilities to the Elastic Search Platform (including Elasticsearch and Kibana) and its three built-in solutions — Elastic Enterprise Search, Elastic Observability, and Elastic Security. With Elastic 7.15 comes the general availability of the Elastic App Search web crawler and tighter integrations with Google Cloud — enabling our customers and community to more quickly create powerful n
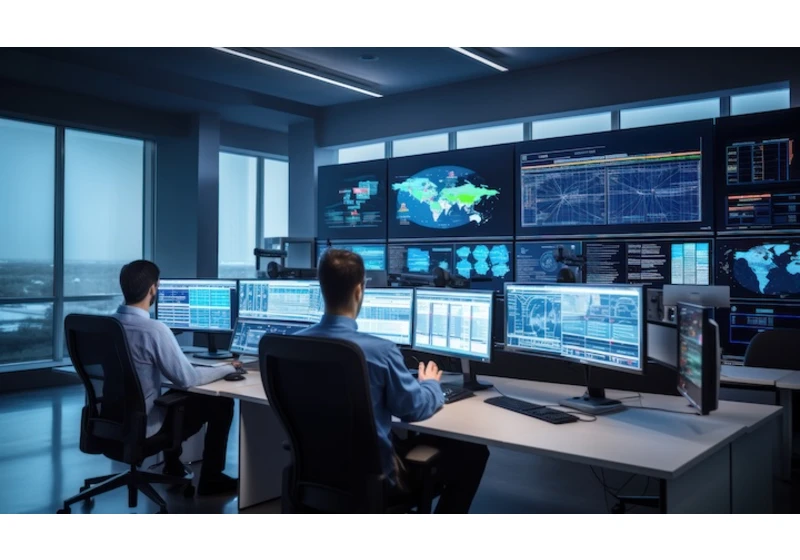
This has been the year of solving: From rapid digital transformation emboldened by the hybrid workplace to substantial cybersecurity attacks disrupting infrastructure, solvers were ready at the front lines. Elastic has been the platform for solvers who are addressing exceptional challenges including: delivering water to 3 million customers, driving insurance innovation, and securing billions in customer assets. And this year’s ElasticON Global 2021 theme, “Solve,” celebrates all of those working

Version 6.8.19 of the Elastic Stack was released today. We recommend you upgrade to this latest version. The 6.8.19 patch release contains fixes and small enhancements for the stack. For a full list of changes for each product, please refer to the release notes: 6.8.19 Release Notes Elastic Stack
Elasticsearch Kibana Beats Logstash

Version 7.14.2 of the Elastic Stack was released today. We recommend you upgrade to this latest version. The 7.14.2 patch contains fixes and small enhancements for the stack. For a full list of changes for each product, please refer to the release notes: 7.14.2 Release Notes Elastic Stack
Elasticsearch Kibana Beats Logstash
Elastic Enterprise Search
Enterprise Search
Elastic Observability
APM
Elastic Security
Elastic Security Solution
We are thrilled to announce the second public alpha of 8.0.0 just a month after the first one. Again, we want to remind you that this is an alpha version. We recommend that you keep it an arm's length from production. There is no guarantee that 8.0.0-alpha2 will be compatible with other preview releases or with 8.0.0 general availability (GA).Also, 8.0.0-alpha2 will again not be available on Elastic Cloud. But, we expect to make a preview version available in the coming months, so you can also h
To monitor your Elastic Stack with Elastic Cloud on Kubernetes (ECK), you can deploy Metricbeat and Filebeat to collect metrics and logs and send them to the monitoring cluster, as mentioned in this blog. However, this requires understanding and managing the complexity of Beats configuration and Kubernetes role-based access control (RBAC). Now, in ECK 1.7, the Elasticsearch and Kibana resources have been enhanced to let us specify a reference to a monitoring cluster. When specified, sidecar cont

We proudly celebrate Hispanic and Latinx-identified communities as part of Elasticians Unidos Month, a global expression of solidarity and appreciation of Hispanic Heritage Month. Employees at Elastic have come together to extend the US Hispanic Heritage Month to communities around the world of Hispanic and Latinx identities through a series of virtual learning and sharing–from ceviche and tortilla making to folklore and history-telling, from music showcases to cocktail mixings. To kick of

We are excited to announce that Elastic Observability has earned the Enterprise Management Associates Top 3 Award for Observability in 2021, a recognition of our commitment to empowering customers with products and features that advance digital transformation and solve real-life problems.
"Elastic Observability with rich analytics and machine learning capabilities allows development and operations teams to get contextualized information that cuts through the complexity, enabling users to quickl