I have been working in the IT industry for over 30 years, for most of this time as an editor at PC-WELT (PCWorld’s German sister publication), specializing in security. I test antivirus software, give tips on how to make Windows more secure, am constantly on the lookout for the best security tools, and monitor the activities of cyber criminals.
Over the years, I have acquired a whole range of behaviors and principles that seem completely normal and sensible to me. However, when I observe other PC users, I often discover risky or at least less security-oriented behavior.
That’s why I’ve put together the 10 most important things I would never do as an IT security expert, with tips on what to do instead.
Further reading: Installing Windows 11 on old PCs is incredibly risky. Here’s why
1. Move instead of copy
You can hardly tell the difference in Windows Explorer: Here, photos and videos are moved instead of copied. This can worsen data security rather than improve it.
IDG
Moving your own files instead of copying them immediately makes me feel uneasy. This includes, for example, photos or videos from the camera or audio recordings from a smartphone or audio recorder. If you move such files, which are usually unique, you run the risk of losing them as soon as you move them. Although this is very rare, it cannot be completely ruled out.
But even if the moving process goes smoothly: The data is then still only available once. If the hard drive in the PC breaks, the data is gone. If I make a mistake and accidentally delete the files, they are gone. These are risks that only arise if you start a move operation instead of a copy operation.
If you think “I need the space on the SD card for new photos,” then you should consider buying a second SD card. Your own data is always worth it.
And when do I release the space on the SD card? I do this as soon as my backup plan on the PC has backed up the copied data. In my case, this is done on a hard drive in the network that runs on a Raspberry Pi.
Important files are also automatically encrypted and uploaded to cloud storage.
Further reading: Best online backup services
2. Save my own data without a backup
I have set up an automatic backup for all important data. Because saving files I have created myself without a prompt backup is far too risky for me. This also includes all data that I enter into apps, for example, whether for Android, iOS, or Windows. Just because most apps don’t offer an easily recognizable backup function doesn’t absolve the user of responsibility for their data.
great windows backup software
For example, at two grammar schools in Koblenz, Germany, several hundred school iPads were logged off the school network due to an error. The handwritten notes in the Goodnotes app used by the pupils were deleted. Many students had worked exclusively with the school’s own iPads and this app — in other words, there was no secondary copy of their notes. Around 500 of the total of 7,500 iPads were affected by the data loss by being connected to the school network at the time of the breakdown.
A cloud backup, as is usual for iPads, was deactivated for data protection reasons. No other form of data backup appears to have been used. The pupils concerned cannot be blamed here, but the system administrator responsible can.
3. Format storage without a thorough check
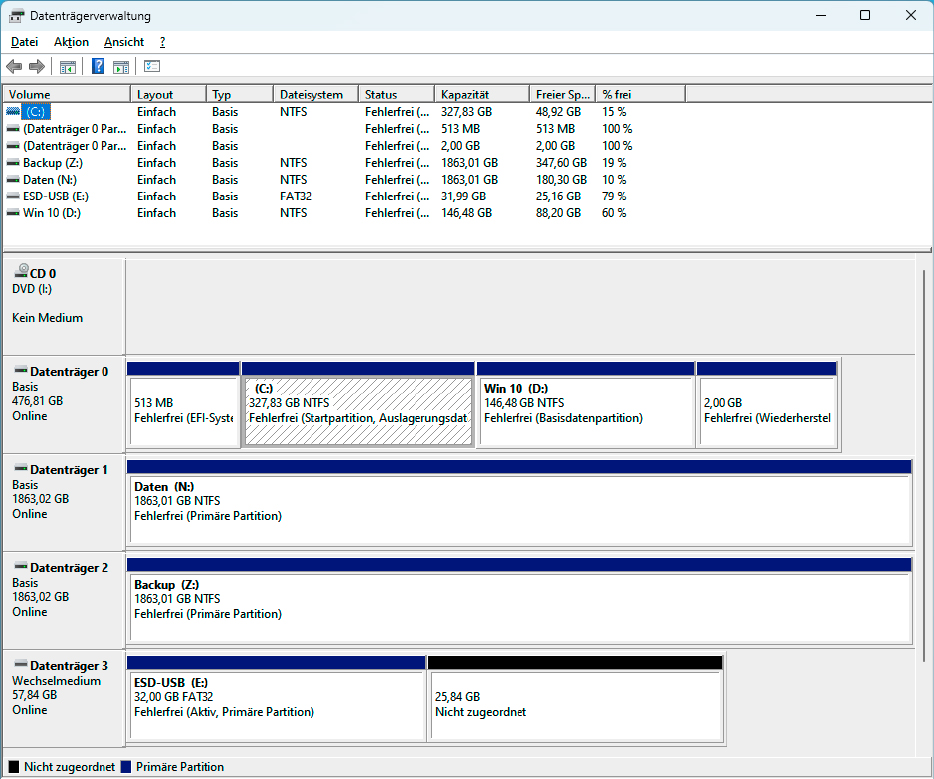
The drive management shows each connected drive with all partitions. You can usually clearly identify a partition based on its name and size.
IDG
I would never make this mistake — because I have made it before. Therefore, I can only advise from experience: Only format a storage drive when you are sure that you have selected the correct drive.
For years, I used external USB hard drives to store my files. The folder structure on these hard drives was usually identical. There were the folders “My Documents,” “Videos,” “Temp,” “Virtual PCs,” and a few more. What’s more, all the hard drives were the same model, which I had once bought generously on a good deal. Some of these disks even had the same data carrier designation — namely “Data.”
That wasn’t very clever, because it made it too easy to mix them up. So I ended up confusing one of these hard drives with another one at a late hour and formatted the wrong one.
Since then, I have named and labelled my external hard drives and USB sticks very clearly and take another close look before formatting them.
First check, then format: Choosing the right drive before formatting is crucial to avoid unintentional data loss. In Windows Explorer, check which drive letter the hard drive or partition to be formatted has. This is often not immediately apparent on systems with multiple drives. Take the time to check, unplug other hard disks and drives to increase the overview. The name of the disk and its size will help you to identify it.
In addition, start Disk Management by entering Disk Management in the Windows search. All connected disks and their partitions will be displayed. Only start formatting when you are sure that you have found the correct hard drive, USB stick, or partition.
4. Open links in emails
I don’t like to open a link in an email. And I never open a link if the email is supposedly from my bank or payment service provider. I don’t even open the link in the monthly email from PayPal, even though I know that this email actually comes from PayPal.
Why not? Nowadays it is very easy for an attacker to create a deceptively real copy of a bank email. I wouldn’t reliably recognize the difference between a phishing email and a real bank email — at least not in the short time I have to check my inbox.
Instead, I open online banking pages and other important pages via links I’ve saved in my browser, or retype the address into the browser each time. I log in to the site and check whether a new message has arrived in my customer account. If not, then the message in the email is either a fake or not important enough for the bank to enter this information in my customer account. That’s the end of the matter for me.
Tip: Change these 5 Windows settings to improve your data privacy
5. Opening suspicious files
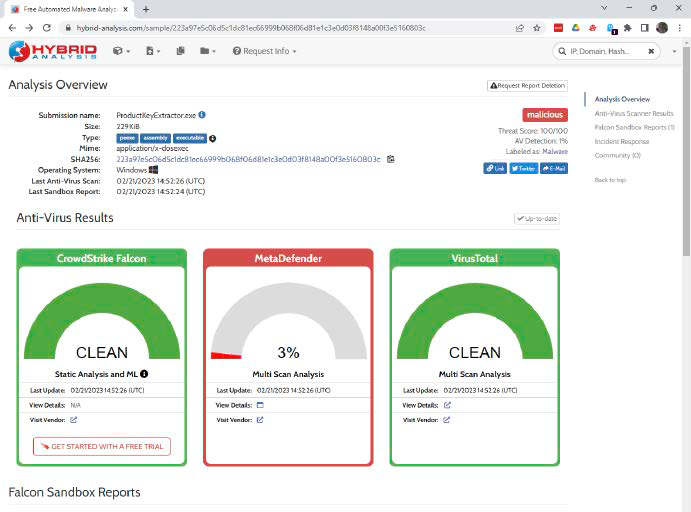
The online sandbox Hybrid Analysis documents the behavior of a suspicious program with a screenshot. The service is free, but it is often overloaded and responds very slowly.
IDG
If a file is suspicious, regardless of whether it’s a program or a document, I don’t open it. The risk is simply too great. As an IT editor, I am of course constantly downloading tools from the internet and quite a few of them are scanned by the virus scanner. That is one indication that makes a file suspicious.
Another is the source. Files from dubious websites are just as suspicious as files that are attached to an email or come from links in emails. If I can’t avoid opening or starting such files, I always check them first with the tool
Autentifică-te pentru a adăuga comentarii
Alte posturi din acest grup
The year ahead has a lot in store for Linux users. Many of the trends
Countless cables are used in the home — whether for charging smartpho

With just a few days left of the year, we found an amazing deal for t

Thunderbolt 5. The cutting edge of I/O. All of it — monitors, a Thund

Picture this: You receive an audio message from your sister. She says

In this yearly penultimate episode of The Full Nerd, Brad Chacos, Ala